How to Stop your Personal Information Leaking to the World

At some point you have probably shared too much online. Here’s how to reclaim some privacy and make sure your Facebook, Twitter and LinkedIn aren’t leaking private information.
The internet can be an obnoxious place, and the sharing culture of social media often runs counter to security and privacy best practices. Most of us have at some point shared our birthdays, photos of our loved ones, information about where we live and come from, and other content that perhaps shouldn’t be made public online.
In a worst case scenario, information you share online could be taken advantage of to pose a threat to your security or even physical safety. The fundamentals of securing your online presence are much the same regardless of what online services you use.
Before we get on to specific actions for Twitter, Facebook and LinkedIn here’s what you should be aware of if you’re looking to better protect yourself online and make sure your information has a smaller chance of being abused.
 |
| Protect your data! |
In general you should ensure that mutual friends/followers with access to restricted accounts are people you trust. Search your post history for personal information that could be used for identity theft, to access your accounts, or to locate your physical address. If necessary, take measures to remove them en masse. Plus you can check for photos of you that others have shared on tagged, removing any tags if they are unneeded.
When it comes to protecting your physical address, this can be exposed in a number of ways. If you’re an eBay seller and have shared links via personal accounts, note that your address is generally published alongside your auctions. The same may apply to other business listings, such as records at Companies House, as well as some academic listings.
If you’re being actively threatened, it’s best to immediately restrict access, set private or, if necessary, suspend, delete, or unpublish your accounts. While doing so you should screenshot and report any threats that have been sent to you, before blocking those who are responsible.
Other steps you can take are: disabling automatic location sharing, enabling two-factor authentication to protect your accounts, back up and delete old posts wherever possible, and consider closing non-essential social media accounts that you don’t use anymore and particularly those associated with your real name and identity.
Now for some specifics.
Twitter:
 |
Twitter’s security recently came under scrutiny when someone social engineered their way into the site’s admin panel, allowing them to access and post cryptocurrency scams from some of the site’s biggest verified accounts. None of the measures below can protect you if the social network itself is compromised, but they can help keep you safe from more typical threat vectors.
Within Twitter itself, make sure location tagging is off on your tweets in Settings > Privacy and safety > Location information. This can get turned back on accidentally if you re-install the mobile app, for example, so it’s worth checking every now and then.
Under Discoverability and contacts, disable email address and phone number discoverability. This will stop people looking up your account using your other personal information – something that’s crucial if you’re wishing to post anonymously.
If you tick Protect your tweets on the main Privacy and safety screen, only people who follow you will be able to see anything from your account, past or present. They also won’t be publicly searchable. Receive messages from anyone in the Direct messages section is unticked while you’re here and disable photo tagging.
Twitter is aggressively hard to work with if you want to delete many tweets or unfollow lots of people – to the point where the official recommendation is to create an entirely new account and swap usernames.
However, a number of third-party tools, such as TweetDelete and Tweepi, make it easier for you to unfollow multiple users and delete large numbers of tweets at once. Be aware that limitations to Twitter’s API mean that it may take a significant amount of time to unfollow hundreds of people or fully delete a long-lived account’s posting history.
Back your posts up before any such tools by downloading your Twitter data via your account settings and remember to revoke any such tools’ access to your account once you’ve finished with them.
Various tools also exist to export your followers. The Twlets Twitter to Excel Chrome extension is a conspicuously easy option, but you’ll have to register and, if you want to download the details of more than 1,000 followers, either subscribe or buy credits. Martin Hawksey’s Twitter-exporting Google Sheet is free but requires you to set up a developer account and create an API key.
Alternatively, create a new account and just go through everyone you’re following on your old account before deleting it or locking it.
Facebook:

You’ll find Facebook’s main privacy options on the settings screen. Under the security and login tab, you should enable two-factor authentication, check what devices are logged in and enable alerts for unauthorised logins if you suspect someone may try to break into your account.
Under the Privacy tab, you can set who can see your posts, including your old posts – set both to friends-only or private. You should also set your friends list visibility to Only me or Friends, disable email address and phone number based lookups and possibly restrict friend requests to only people who are already friends of your friends.
These settings also include an option to review past posts. This will take you to your Activity log, where you can see everything you’ve posted, as well as anything others have tagged you in. You can also get to the Activity log by clicking on the downward-pointing arrow at the far right of Facebook’s top toolbar, clicking Settings & privacy and then Activity log.
On Activity log, click Timeline review, then Posts. You can select them by date, shown along the left-hand navigation bar. Use the ‘…’ icon at the top right of each post to delete them one by one. However, if you use Facebook or Facebook Lite on your phone, you’ve probably received access to the Manage Activity feed, which lets you send multiple posts to a Trash bin, from which they can be recovered for 30 days before being fully deleted.
From your mobile Activity Log page, tap Manage Activity at the top. You can then filter your past posts by date and content, and use tick-boxes to select multiple posts to delete or privately archive. If you’re had your account a long time, full deletion will still be time-consuming, but it’s a good way of keeping on top of a regular deletion habit.
Also on mobile, disable location servicesto avoid inadvertently advertising your movements.
If you need to get rid of your full posting history you may still wish to use more convenient third-party tools such as the Delete All Messages for Facebook and Social Book Post Manager for Chrome. Be aware that the effectiveness of such tools is dependent on factors including Facebook not changing its API and the speed of your internet connection. As ever, back up your data before deletion and remove the tools from your browser when finished.
If you plan on closing or temporarily deactivating your account, you’ll find those options in the Your Facebook information tab, as well as an option to download a full archive of all your posts and activity on the platform – you should also take advantage of this before bulk deleting posts.
Facebook’s tools for viewing and unfriending the people are also easier to work with than Twitter’s: from your main profile page, click on your Friends tab to browse through them and click on the Friends label next to someone to produce a drop-down and click Unfriend to remove them. Sadly, we couldn’t find any functional tools to automate this process.
LinkedIn:

By its very nature, your LinkedIn CV – or any other online CV you may have – can reveal a huge amount of information about where you work, where you live and how to get in touch with yourself or your employer.
It’s a very good idea to remove any unnecessary email addresses or phone numbers, particularly those you primarily use for personal matters, and use LinkedIn’s Privacy Settings to set your profile private, choose whether or not people outside your contact network can see your name, remove any linked social media accounts and change your geographic location data. It’s also a good idea to set information such as your date of birth visible to Only Me using the edit (pencil icon) option on your main profile.
You can also close or temporarily deactivate your account. Once you’ve locked down a few basic security settings, such as restricting who can see your email address, the main thing to check is what personal information your CV might reveal.
LinkedIn is trying muscle into more conventional social networking territory. If you’ve used this and wish to delete your posts, go to Me > Posts & Activity to see your entire activity feed. Unfortunately, you’ll have to delete posts one at a time, as there are no mass deletion options here.
Information in the wild
Massive data breaches are an unfortunate fact of online life. Visit Have I Been Pwned to check whether your email addresses, passwords or other personal data have been exposed in any breaches.
As a priority, make sure you’ve changed your password for the breached services and that you haven’t reused it anywhere else. Unfortunately, there’s not much you can do about most stolen personal data except be aware of the fact that it may now be out in the wild out there.
If you’re concerned about real names, phone numbers or addresses being discussed in connection with your online handles, run the terms through a couple of search engines together. If you’re concerned about this information being published online, you can create a Google Alert to email you if it shows up.
Check your websites, those of your employer and of any academic institutions, clubs or charities you work with to ensure that they’re not sharing too much personally revealing information about you. Finally, anywhere online where you don’t need to be personally identifiable, use a pseudonym.
WhatsApp:

In the summer of 2016, WhatsApp made an unprecedented change. The Facebook-owned company turned on end-to-end encryption by default for all of the billion-plus people using it and in the process became the world’s biggest encrypted messenger. Since then the number of people using it has swelled to more than two billion.
The radical shift means that nobody at Facebook is able to read, or mine data from, the content of the messages you send. The only things that can access them are the two phones – acting as endpoints in the encryption setup – where the app is installed. For the encryption protecting your messages to be decoded, both devices must verify and exchange security codes as messages are transferred.
The encryption WhatsApp uses comes was originally developed by Open Whisper Systems, the group behind encrypted messaging app rival Signal. Even though WhatsApp’s end-to-end encryption does protect your communications – including files, images and calls – that doesn’t mean the service is as private as it could be by default. In fact, when it comes to WhatsApp versus Signal, we recommend the latter for people wanting the maximum security and privacy options.
However with more than a third of the world using WhatsApp, its popularity is unrivalled and you may not be able to drag all of your friends, family and groups across to Signal. If that milestone is still some way off, here are some tips to make WhatsApp as private as possible.
Understand what WhatsApp collects
WhatsApp can collect a lot of information about you that you may not fully realise. Much of what it collects is similar to any other app and can be found in its privacy policy. But the app is also part of Facebook’s machine and this information can be combined with other data you give Facebook, through the social network but also its other products, including Instagram.
WhatsApp says your phone number from WhatsApp, device information (including the type of phone, mobile country code, and operating system), and some of your usage information (when you last used WhatsApp, when you registered and how often you message) are shared with other Facebook companies. Some of this data sharing has been controversial: in May 2017 the company was fined £94 million by the EU for combining WhatsApp phone numbers with Facebook data after it told regulators it couldn’t easily be able to do so.
Any data sharing may come under further scrutiny in the future as Facebook looks to merge the infrastructure between WhatsApp, Facebook Messenger and Instagram’s messaging. However, it’s worth stressing that the content of the messages you send isn’t shared, as Facebook doesn’t have access to them due to WhatsApp’s end-to-end encryption.
WhatsApp collects more information about you than it shares with Facebook. Most of this is metadata, which can be revealing about user behaviour. The company’s privacy policy says it gathers information about how you interact with others on its services (the time, frequency and duration of interactions with others), some diagnostic information about when the app crashes and other information such as any statuses you set, group features, your profile photo and when you’re online.
On top of this WhatsApp may also collect information about your phone’s battery level, signal strength and mobile operator. Location information, when you turn it on, is also collected and there are cookies that track your activity within the desktop and web versions of the app.
Turn off cloud backups

WhatsApp allows you to backup your chats and data as a handy way to move all your information to a new phone – although this doesn’t actually work if you’re moving from iPhone to Android. These backups work by storing your data in Google Drive or Apple’s iCloud, depending on which operating system you use.
WhatsApp wants you to backup your data – if you don’t have the setting turned on it’ll prompt you to start backing up every few months. But there’s a very good reason why you shouldn’t back everything up to the cloud. The backups of your messages aren’t properly encrypted. That means if they’re accessed by someone else, the messages can easily be read. The process sort of defeats the point of the initial end-to-end encryption.
For instance, a law enforcement request to Google or Apple can see them handover the backed-up chat logs and the messages revealed. This does happen too. In June 2018, former Donald Trump campaign chairman Paul Manafort, who is now a convicted felon and in home confinement serving a seven-year sentence, had his WhatsApp messages accessed through a federal request for his iCloud data.
Unencrypted backups on WhatsApp has been an issue for years and it’s one the company knows about: some reports state WhatsApp is testing password-protected backups, but these have not been widely rolled out or officially announced by the company.
Turn on two-factor authentication
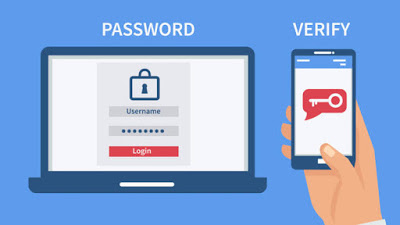
You should be using two-factor authentication as much as possible – it’s even more important on accounts that hold your sensitive personal information, such as photos and messages. The security method involves adding an extra step to the process when you log in to an account. In most cases, this involves using a security code generated by an app, a code sent via SMS or a physical security key. (The last of these is the most secure way to protect your accounts with two-factor authentication)
Using WhatsApp is different to logging-in to your email. It’s likely that you’ll access the app multiple times a day – on average I open the app between 50 and 80 times per day. Entering a security code every time this happens would be impractical and frustrating. So instead, WhatsApp’s two-factor authentication, which can be turned on through the settings menu and then by tapping on account, uses a PIN.
WhatsApp will semi-regularly ask you to re-enter the six-digit PIN you create to access the app. It doesn’t say how often these prompts happen but they’re irregular enough not to be a barrier to using the app. The PIN will also be required any time there is an attempt to add your number to a new phone or device. When you’re setting the PIN there’s also the option to add an email address that can be used to rest the code if you forget it.
Stop people seeing your personal info
WhatsApp spam and social engineering attacks, devised to steal your personal information, exist. Every few weeks a new scam will circulate where attackers are looking to compromise accounts. WhatsApp has even threatened legal action against those to hit users with colossal amounts of messages.
There are a few steps you can take to limit ways people can interact with your account and have access to your personal information. These are all found through the settings menu, followed by tapping on account and privacy. At the most simple you can turn off read receipts, the two blue ticks that show when someone has seen your message and is now ghosting you.
More effective are the steps that stop people adding you to groups. Under the groups setting there is the option to limit who can add you to a group: by default, this is set as ‘everyone’. However, it can be changed to all of your contacts, or all of your contacts except some people who you block from doing so. Deciding to limit who can add you to groups doesn’t mean that you can’t join groups when people aren’t in your contacts. Instead, people wanting to add you to groups can request to do so via a separate message.
You can also turn off who can see your profile photo, the ‘about’ section, WhatsApp status, and the time when you last looked at the app. When in the privacy settings you should also check whether you are sharing your live location with anyone.
If you’re going for the most private approach, it’s also worth considering what information you might leak through your phone’s screen. New message notifications can include the entire message, or some of its content when they flash up on your screen. If these notifications also sit unread, anyone picking up your device may be able to read them without having to unlock the phone.
Notification settings sit outside the WhatsApp app. To change these you’ll need to go to iOS or Android’s settings and into the notifications options, where previews of messages can be turned off. It’s likely that you’ll need to do this for each app individually.
Switch to Signal
If you’re looking for more privacy, switching messaging app is a big upheaval but could be worth the time and effort. As mentioned earlier, our preference for combining end-to-end encryption with greater levels of privacy is Signal. The app allows you to lock it and use facial recognition or fingerprint sensors to access messages, messages can be made to disappear after a certain amount of time and it’s possible to blur the faces of people in photos and videos.
You can visit our telegram channel for more information http://t.me/droidvilla